Introduction
In order to fully utilize a system, whether it is a Document Management System (DMS), Enterprise Resource Planning (ERP), Customer Relationship Management (CRM) or any other, it needs to be integrated with existing systems or third-party solutions.
System integration, in this case, HTTP integration, refers to the use of HTTP to communicate and exchange data between different software components and applications.
To put it in simple terms – HTTP is like a language that both sides understand and that ensures two systems can exchange the data. Just like two people using English to communicate with each other.
HTTP integration, on the other hand, refers to different programs using that language to talk to each other and work together, like people from different countries/language areas who can still communicate with each other by speaking a language they both understand.
Here we’ll show how you can integrate M-Files with external systems simply and securely using HTTP integration.
Main HTTP methods
Data exchange, or integration may seem complicated, but breaking it down to its basics, there are four main HTTP methods:
- GET
- POST
- PUT
- DELETE
Let’s dive into each of them.
- The GET method is used to retrieve information from a server. It is the most widely used HTTP method and it is used to request information from a resource, such as a web page or an image. The GET method is considered to be safe and idempotent, meaning that multiple identical requests should return the same result.
- The POST method is used to send information to a server for processing. It is used to submit data to a resource, such as a form submission or the upload of a file. Unlike GET requests, POST requests can modify the state of the server, and therefore are not considered to be safe or idempotent.
- The PUT method is used to update an existing resource on a server. It is used to replace an existing resource with a new one, and is also considered to be idempotent.
- The DELETE method is used to delete a resource on a server. Multiple identical requests should result in the deletion of the same resource.
By using only these four actions, you are able to bring a lot of value to your end-users.
HTTP integration with M-Files
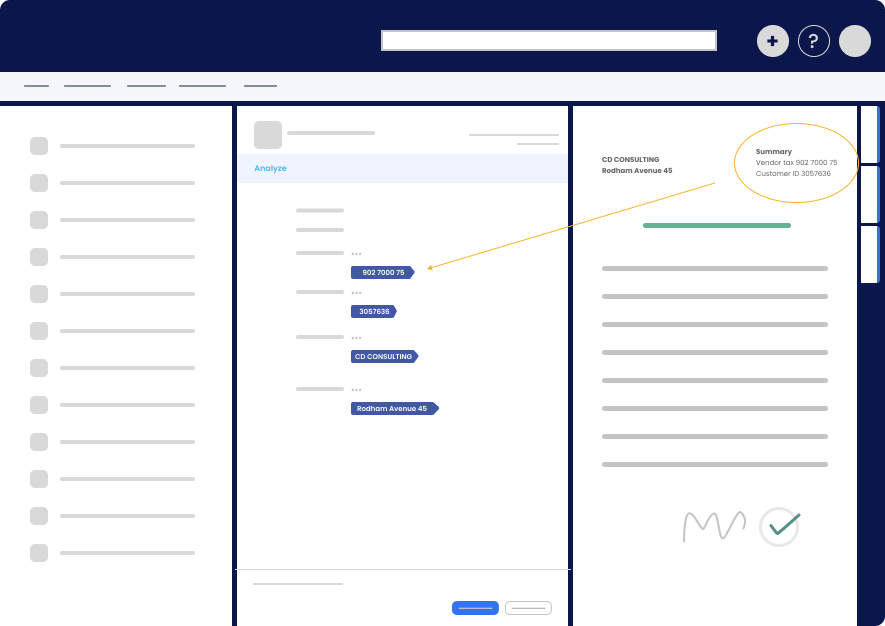
Now let’s put all of the above into the M-Files environment and see how we can integrate M-Files with other systems using the Extension Kit and its HTTP integration module.
Extension Kit is a solution that provides additional functionalities to M-Files, including HTTP integrations, without the need for custom coding. The HTTP integration module supports four fundamental HTTP methods (GET, POST, PUT, DELETE) which are essential in establishing a seamless connection between M-Files and other systems.

*Picture 1: Extension Kit supporting main HTTP methods*
Thus, with the Extension Kit, you can easily and efficiently integrate M-Files with third-party systems for any desired use case, without any coding. The key benefit of using the Extension Kit is that it eliminates the need for custom coding and provides a straightforward and errorless setup process.
What is your body type?
Now that we know the language we speak and who we want to exchange the information ‘back and forth’ with, let’s talk about the “tone of the voice” we can use while making all of this happen. What we’re trying to say is that there are certain formats in which the data is being transferred between two systems. We referred to it as “a tone of the voice”, but you will find it more often as the message body or body type.
To successfully transfer the data, both systems should know how to interpret the data sent from one service to another. In order to do that, there are several standard body types used. Note that body is sent only with POST and PUT methods. HTTP Integration supports:
- JSON
(JavaScript Object Notation) is a lightweight data-interchange format. It is easy for humans to read and write, and easy for machines to parse and generate. JSON is used to transfer data between a client and a server in a text format.
- XML
Extensible Markup Language (XML) is a markup language and file format for storing, transmitting, and reconstructing arbitrary data. It defines a set of rules for encoding documents in a structured format that is both human-readable and machine-readable,
- RAW
Raw data can consist of anything. As the name suggests: raw, unprocessed data.
- FORMURLENCODED
The URL-encoded data sends encoded data to the server, and uses the same encoding as that of the URL parameters.
XPATH and JSON Path
To be able to successfully parse the data on the M-Files side, Extension Kit supports both XPATH and JSON Path query languages.
XPATH
XPath uses path expressions to select nodes or node-sets in an XML document. The node is selected by following a path or steps.
Example
/customers/customer[age>35.00]
JSONPath
Query language for JSON, similar to Xpath for XML. Allows you to select and get data from JSON document.
Example
$.customers.customer[0].email
Security in the first place
There is no system integration without the right security in place. We are witnesses of more and more security attacks in the world. As a result, Security Engineer has become a very hot role in the labor market, and with companies being more aware of the importance of security, it is here to stay.
In order to be able to support integrations with as many systems as possible, Extension Kit HTTP Integration module supports all relevant security standards.
OAuth 2.0
OAuth 2.0 is the industry-standard protocol for authorization. It focuses on client developer simplicity while providing specific authorization flows for web applications, desktop applications, mobile phones, and living room devices.
Basic
Simplest technique for enforcing access controls to web resources in case your legacy systems only work with this type of authentication.
Digest
Unlike Basic, Digest authentication does not required sending the username and password with every request. MD5 hashing algorithm is used and has is sent together with username.
NTLM
Windows New Technology LAN Manager – suite of security protocols offered by Microsoft to authenticate users´ identity.
Kerberos
Kerberos is a protocol for authenticating service requests between trusted hosts across an untrusted network. It support is built in to all major computer operating systems, including Microsoft Windows, Apple macOS, FreeBSD and Linux.
Negotiate
Negotiate authentication automatically selects between the Kerberos protocol and NTLM authentication, depending on availability.
ApiKey
Some APIs use API keys for authorization. An API key is a token that a client provides when making API calls. The key can be sent in the query string, request header or as a cookie.
Conclusion
HTTP plays a crucial role in web-based application development, enabling various systems to exchange information and data in a standardized format.
The ability to integrate different systems through HTTP enables organizations to build complex and scalable systems that can be easily maintained and extended.
M-Files as an Intelligent Document Management System can be fully utilized if exchanged with other systems. That is what Extension Kit for M-Files is for. With the support of four main HTTP methods and various standard body types, the Extension Kit ensures successful data exchange between systems.
Additionally, the support for XPATH and JSON Path query languages, and the various security standards, make the Extension Kit a secure and reliable choice for system integration.